How Physical Access
Becomes Digital Control
HuFiCon Management Memo:
Journey with the CISO
A mountain climb to cyber security resilience. Find out how to get to the summit of cyber security resilience in Inge van der Beijl's management memo, from her presentation at the Human Firewall Conference (HuFiCon) on the 14.11.2024.
The climb will take you from the base camp of foundational security to the high-camp of a security conscious culture, all the way to the summit consisting of strategic security integration.

Inge van der Beijl
Director Innovation

Lessons learned from the Cyberattack at the port of Antwerp
Organisations today face an attack surface that extends well beyond traditional IT. Physical operations, IT systems, supply chains, and OT environments are now deeply intertwined, creating an expansive, attractive target for hybrid attacks.
The 2020 cyberattack on a busy cargo terminal at the Port of Antwerp is a clear early example of this shift. One small intrusion–a USB drive inserted into a computer–ultimately enabled large-scale supply chain abuse. Investigators say the compromise was part of a wider organised drug trafficking scheme affecting multiple European ports, including the Port of Rotterdam.
When the attack was finally exposed in 2021, a cyber forensics investigation revealed a technically unsophisticated attack that relied on basic, noisy, and well-documented malware and techniques. And yet, the threat actor succeeded by exploiting physical access, insider trust, and weak separation between IT systems and OT environments.
Five years later, we believe this case is more relevant than ever.
Northwave’s Cyber Threat Intelligence recently examined how nation-state actors are targeting the expanded, cyber-physical attack surface in Europe. At the same time, our Global Threat Landscape Report explores a parallel trend: traditional organised crime adopting the same hybrid techniques, particularly where OT environments and supply chains are involved. Ports, logistics hubs, and industrial operations sit squarely at the centre of this risk.
In this article, we dissect the full kill chain of the cyberattack at the Port of Antwerp terminal—in, through, and out—to show how digital and physical domains merged. Then, we examine what organisations across industries can do to defend their operations against today’s adversaries.
Note: All information shared in this report has been drawn from publicly available sources, including court records and media publications.
Timeline
15-17 September 2020
Hacker and accomplices discuss plans for a malware attack at a container terminal in the Port of Antwerp
Terminal employee agreed to insert a malware-infected USB stick into a terminal computer for a €10,000 fee
Source: Court of Appeal of Amsterdam
Insider Compromise and Social Engineering
Instead of hacking the network firewall, the threat actor targeted the human firewall, taking advantage of trust and access inside the organisation. A terminal employee was paid 10,000 euros to insert a malware-infected USB stick into her computer at a large cargo terminal in the port of Antwerp. The malware enabled a hacker to access the terminal systems and maintain persistence. This aligns with what we see in many cyber incidents: whether insider compromise is malicious or unintentional, human access is often the vulnerability that threat actors can exploit with ease.
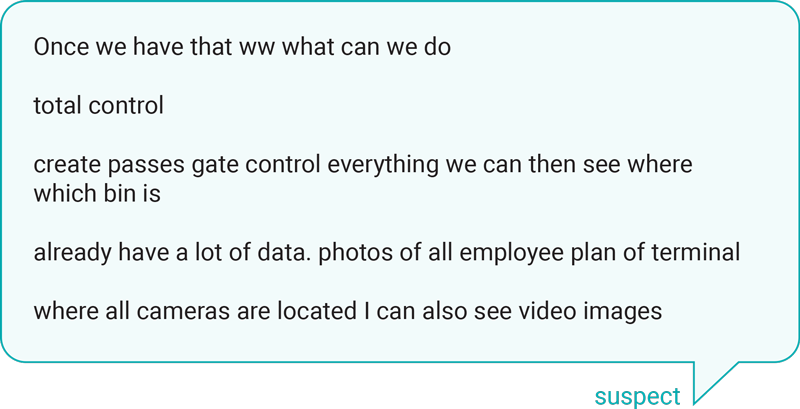
Court records of phone conversations between the hacker, referred to as “suspect” by the court, and his accomplices provide deeper insights into the planning and execution of the attack. In the weeks leading up to the cyberattack, an accomplice (referred to as Sky number 5 in court records) discussed the goal of having a computer under control to open the terminal gate so a truck could enter.These early discussions reveal the confidence the hacker had in his ability to swiftly breach the terminal’s cyber defences and stealthily move through the network system.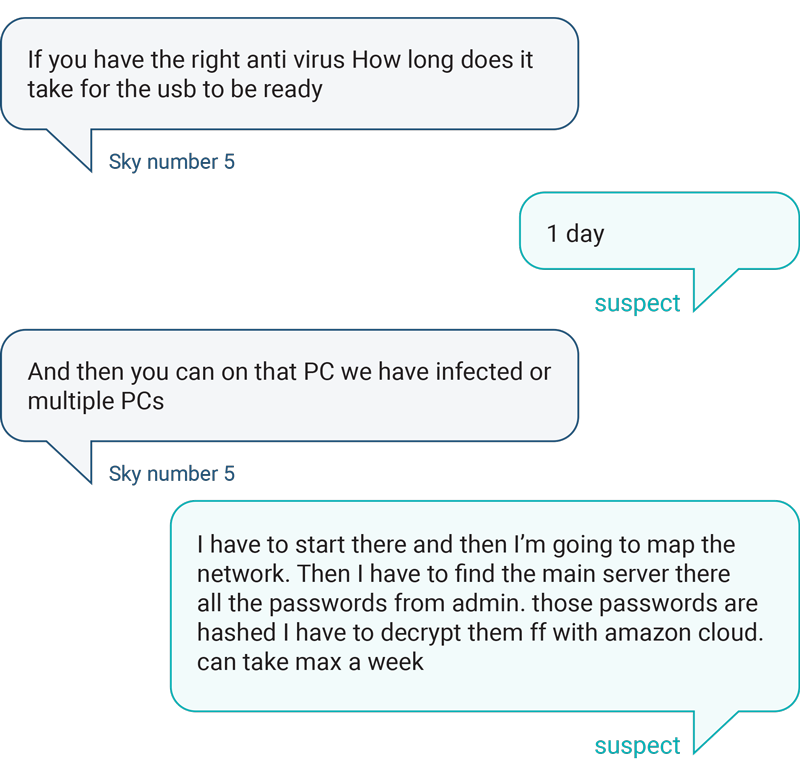
Decrypting Organised Crime
The hacker used SkyECC phones to communicate with the terminal employee “insider” and other criminal accomplices. This strategy would later deliver crucial evidence in the case. Since the Sky Global company promised limitless privacy with their encrypted phones, the criminals freely discussed their activities. But that wall of privacy came crashing down in early 2021, when a joint effort by law enforcement from several countries enabled them to access millions of messages sent through the encrypted phones. This breakthrough led to arrests and convictions of dozens of drug traffickers and other organised crime figures across Europe.
Timeline
18 September 2020, 15:20:41
USB stick inserted into terminal computer
Malicious activities begin in the system within seven minutes
Source: OCCRP
Physical Malware Delivery
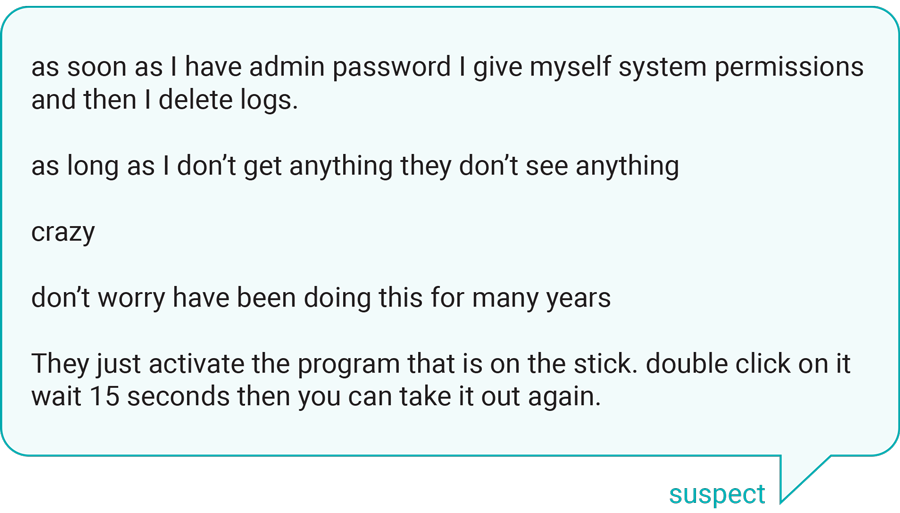
The cyber forensic investigation found that on September 18, 2020, a Sandisk Ultra USB stick was physically inserted into a computer located at the terminal gate. Within minutes, a scheduled task was installed on the system that ran a malicious file and launched several activities, including granting the threat actor remote access of the system and installing a persistent backdoor to maintain access. However, getting through the terminal network proved tougher than the hacker anticipated due to the intrusion detection system.
He then requested more time with the computer on and logged in to get through the firewall and start mapping the system using SSH. This network protocol allows a user to access the computer and gain privileges via a “secure shell” application on the server where the session is taking place.
Timeline
19 September, 12:51:09
Threat actor uses advanced IP scanner to map out the network and look for vulnerabilities
20 September 19:35:40
Deploys nmap mapping tool
21 September 03:52:27
Accesses sensitive data within the terminal’s container management system
23 September 20:15:33
Uses another vulnerability assessment tool, indicating the previous tactics failed
26 September 22:16:50
Uses impacket tool to successfully find a backdoor to exploit. Within an hour, threat actor tunnels from one network machine to another.
Network scanning and reconnaissance
Over the next week, the hacker tried many different ways to gain more system rights and access within the network, also called privilege escalation. He first mapped the network and looked for vulnerabilities using tools that are readily available online. Then, he tried to secure SYSTEM-level privileges with a tool called CVE-2016-7255.exe.
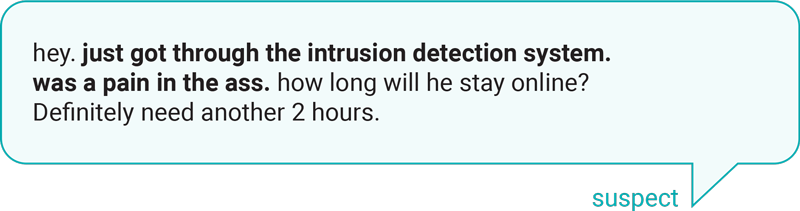
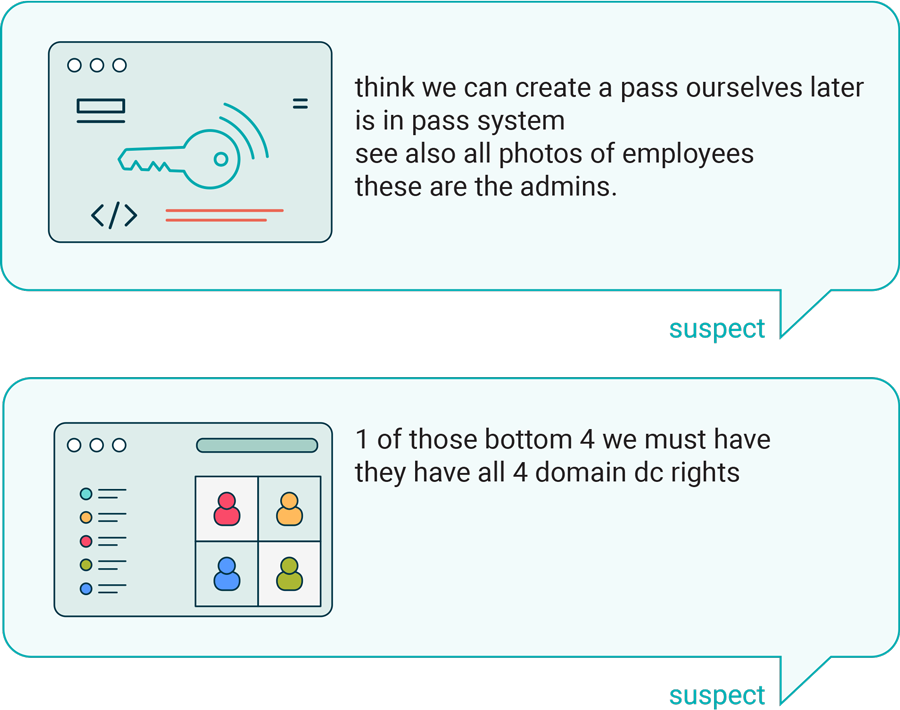
While investigators did not find evidence the hacker was ever able to take over an account with administrative privileges, he did access the software used to manage containers at the port terminal. According to system activity logs, he opened a user manual which would have enabled him to view information relating to staffing and the management and location of shipping containers and their unique PIN codes. Court records of the hacker’s intercepted chats shed light on how much data he was able to quickly access and what he could potentially do with it.
Using a tool called impacket, the hacker finally found a backdoor in the network system that allowed him to bypass security mechanisms. Within an hour, he established a connection to tunnel from one machine in the network to another.

Timeline
27 September 2020
Threat actor located the domain administrator hash, a critical foothold for privilege escalation
5 October 2020
Threat actor says the computer is cracking the hash, costing him €1,000.00 per week
6 October 2020
Threat actor and accomplices discuss ordering a USB keylogger to insert into an administrator’s computer
19 October 2020
Threat actor accesses terminal software to view pages that monitor container vehicles, staff passes, and driver names. Places files in the system that contain lists for a “brute force” attack.
Sources: OCCRP, Court of Appeal of Amsterdam
Credential Theft
The next day, the hacker told his accomplices he had located the “DC admin hash”, the encrypted string that represents the password for the domain controller’s administrative account. In Windows environments, passwords aren’t stored in plain text. Instead, they are transformed into hashes that reside on each machine. Workstations typically store multiple user hashes, but the domain administrator’s hash is often harder to access.
In this case, the malware planted via the USB key appears to have given the threat actor a foothold. From there, the hacker began moving laterally through the network, scanning each machine until he found one that held a domain admin hash in memory. This allowed him to use a technique called “pass-the-hash,” which lets an intruder authenticate without ever knowing the actual password.
But the plan didn’t unfold as smoothly as he expected. A week later, he complained to his accomplices that cracking the hash was costing him €1,000 per week in computing resources–an unexpected challenge that he attributed to the administrator’s long password.
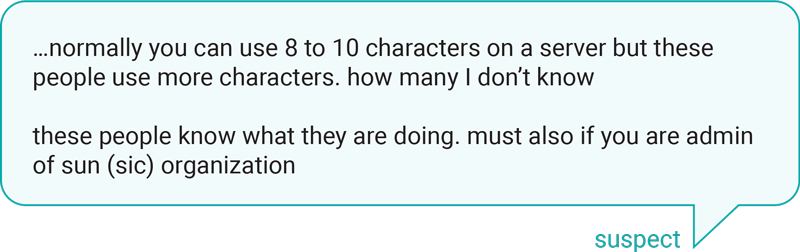
The hacker said if he was still unsuccessful in cracking the hash after another week, his next plan was to put a keylogger on the system that would record keystrokes when the administrator logged in to make updates. Notably, this tactic would have again involved a physical compromise of security at the terminal to insert a different USB in a computer used by an administrator.
Over the following weeks, the threat actor discussed buying a USB keylogger. In mid-October, the hacker added files in the terminal software system to execute a brute-force attack, a method that uses word lists to guess as many passwords as possible.
Timeline
19 January 2021
Threat actor places nearly 1,000 suspicious files on the system in 14 hours, some of which could carry out tasks like running scripts and applications
February 2021
Law enforcement agencies unlock SkyECC phone encryption and begin monitoring 70,000 users worldwide
9 March 2021
Law enforcement in Belgium and the Netherlands arrest a number of criminals and seize evidence in connection to the SkyECC decryption
30 March 2021
Threat actor modifies a user manual for Solvo, but the changes he made could not be recovered
24 April 2021
Last date that the threat actor is definitively known to have been active in the terminal's IT system
Sources: OCCRP, Europol
File Tampering and Persistence
The logs recovered in the investigation indicated the hacker accessed the container software multiple times between October 19, 2020 and April 24, 2021. He visited pages that monitored containers, vehicles, staff passes, and names of transport drivers and installed various suspicious files. This log data reveals the hacker remained undetected for more than six months within the terminal’s IT system.

Timeline
31 August 2021
Chat logs detail ongoing discussions related to drug trafficking at several European ports
September 2021
Hacker arrested on multiple charges connected to the cyberattack at the Port of Antwerp terminal
Source: Court of Appeal of Amsterdam
The threat actor did not have a technical reason to exit the network environment; the backdoor remained active, access was persistent and unnoticed. But the hacker exploited his digital access in the terminal system to influence and compromise physical logistics within the supply chain. The breach of the IT network enabled him to tell drug smugglers when and where to safely pick up drugs that were shipped into the Port of Antwerp terminal. At the port of Rotterdam, the hacker used digital access to monitor how shipping containers were scanned. He sold this information to criminals who could then strategically place narcotics to avoid detection.
Even as investigators were closing in, prosecutors say the threat actor was still discussing transport modes and deck cargoes in late August 2021. Finally, in September 2021, authorities had enough evidence to arrest a 41-year-old man from Rotterdam on multiple charges related to the terminal system hack, extortion, and drug trafficking at several ports.
Authorities believe the cyberattack was connected to a broader pattern of PIN code fraud that enabled at least 200 metric tons of cocaine through to flow through the ports of Rotterdam and Antwerp since 2018. Pin codes are unique reference numbers a shipping company assigns to a container after its transport has been paid. Transporters must provide the correct code along with other documentation to pick up the container from the terminal. Criminals steal or buy these codes for tens of thousands of dollars so they can illegally access and remove cargo from ports. In 2024, the Port of Rotterdam switched to a “Secure Chain” system to curb this kind of fraud.Arrest and Conviction: a unique outcome in a cyberattack investigation
The Port of Antwerp terminal hacker was tried in the Court of Amsterdam and sentenced to 12 years in prison, which he later appealed on the basis that authorities had unlawfully accessed his private SkyECC communications. In January 2025, the court of Amsterdam upheld all but one of his charges–the import of 5,000 kg of cocaine–and delivered a final seven-year prison sentence.
The physical aspects of this case played an important role in the punitive outcome. It’s very challenging for cybercrime investigations to result in a conviction because threat actors typically operate from countries that do not extradite. In contrast, the Port of Antwerp threat actor carried out his activities within the Netherlands and Belgium. This allowed local law enforcement to apprehend, charge, and convict him.

What Defenders Can Learn From The Port of Antwerp Attack
The attack at the Port of Antwerp demonstrated what can very easily happen when a threat actor exploits overlapping vulnerabilities in the physical and digital domains. Five years later, we see even greater exposure and risk in these areas. Hybrid threats targeting EU infrastructure have increased, supply chains have become more complex, and OT environments are more connected than ever through IT systems, IoT and third-party integrations.
For that reason, we’ve outlined four lessons from the Port of Antwerp attack that remain highly relevant, along with concrete actions organisations can implement today.
Cyber incidents occur daily so don’t wait until your organisation is affected. Take a proactive, risk-based approach to strengthening your defences now, based on a continuous understanding of threats and what they mean to your organisation.”
1. Having the basics in order is key
The single most important and impactful thing you can do for your security is cover the basics. Many cyberattacks, especially unsophisticated ones, are preventable with foundational security measures.
These kinds of minimum standards are now, or will soon be, required by law for many organisations. For example, NIS2 requires essential organisations to strengthen cyber resilience and secure supply chains. Additionally, the Critical Entities Resilience Directive (CER) aligns with NIS2 to protect against hybrid attacks, requiring similar improvements to the physical security measures of critical entities. For operational technology (OT), the Cyber Resilience Act (CRA) reinforces requirements for segmentation, access control, monitoring, and lifecycle security across interconnected systems. Even if your organisation is not legally bound to these regulations, rising to their baseline standards will not only strengthen your defences, it will also keep your organisation competitive in the market.
In the case of the Port of Antwerp, we’ve outlined specific basic security countermeasures that would have help prevent the cyberattack on the container terminal.
Here are some important insights on two of these countermeasures:
1. Malicious Insider Awareness
Experts have found that people who commit acts like accepting a bribe to leak data or provide internal access already exhibit suspicious behaviour beforehand. This provides an opportunity for early detection when employees are trained to spot such behaviours and the organisation has a culture that enables safe reporting.
2. Monitored EDR software
The difficulty the attacker faced when trying to break into the Port of Antwerp terminal network indicates an intrusion detection system was present and initially slowed him down. As such, the system–most likely EDR software–was presumably functioning correctly by blocking malicious behaviour. However, when EDR is not installed in a managed setup with a centralised dashboard or alerts aren’t actively monitored, a hacker has all the time and opportunity to bypass it.
The lesson here is that effective defence requires human oversight, ideally through 24/7 monitoring in a SOC, to detect and respond before persistence is established.
Key defender takeaways:
These minimum security standards will benefit any organisation:
- Strong governance & documented cyber security policies
- Identity & access controls (MFA, least privilege)
- Continuous monitoring, detection and incident reporting – including managed Endpoint Detection and Response (EDR) to strengthen real‑time threat visibility and response
- Backup, continuity and disaster‑recovery readiness
- Third‑party and supply‑chain security
- Ongoing cyber safety and awareness training for employees and board-level executives
- Secure product design, patching and vulnerability management
- Physical and operational resilience for critical infrastructure
Any IT system that can alter physical movement, workflow timing, or access decisions is functionally part of the OT attack surface and must be treated as such.”
2. The OT attack surface includes IT & Physical Environments
Compromising operational technology does not require OT-specific tactics. It only requires IT access that is sufficiently connected to physical operations.
Although initial access at the Port of Antwerp terminal occurred on a standard office workstation, the threat actor was able to influence critical processes including logistics and container management–effectively controlling the OT domain. Operations continued normally and no alarms were triggered. Meanwhile, the threat actor quietly tampered with sensitive data. Network boundaries provided little protection because IT identities translated into OT authority.
The cyberattack served to lower the risk of drugs being intercepted at the port or the smugglers getting caught. What once required multiple insiders, risky on-site coordination, and repeated exposure was achieved with one corrupt employee, one USB stick inserted into a single computer, and a truck driver.
Key defender takeaways:
-
Implement default‑deny controls for all removable media, supported by appropriate physical and procedural controls. Ensure alerts are generated for any scheduled tasks created or executed from removable devices.
-
Connect physical security and network data to be able to more quickly identify and respond to coordinated threats. Cross-train teams for crisis situations that include both physical and digital disruptions.
-
OT visibility must include assets, connectivity, high‑risk pathways, and network segmentation controls that limit lateral movement between systems. Make sure privileges across IT, OT, and physical access are separated, tightly scoped, and issued only when needed.
-
Ensure monitoring can detect suspicious but seemingly valid activity, including commands, workflows, or access patterns that are authorised but irregular. In OT, such behaviour reliably indicates operational intent.
The Rise of Cyber-Physical Attacks
Using digital access to make an impact in the physical domain is a strategy that’s not only useful in organised crime. Across Europe, hybrid cyber-physical attacks have surged since Russia’s invasion of Ukraine.
State-aligned groups are targeting transportation networks, government services, critical infrastructure, and industrial operations through coordinated cyber and physical actions. Digital access helps them avoid direct physical confrontation and stay anonymous.
Organisations that do recognise the risk that insider threats pose often struggle with finding the right controls to mitigate it.”
3. Trusted access is easy to abuse
Insider threats, both malicious and unintentional, remain one of the most underestimated risks organisations face today. As we detailed in Northwave’s 2025 Global Threat Landscape Report, despite these incidents being severely underreported, they account for roughly one-third of all data breaches, with the majority caused unintentionally.
Malicious insiders are rare but particularly difficult to detect because they understand internal processes and can blend into normal operations. The stereotypical disgruntled employee only accounts for around 10% of malicious insider cases. In fact, financial stress is a more common driver, prompting some to steal data or accept bribes (Northwave 2025 Global Threat Landscape Report).
This aligns with what the head of the Rotterdam port police has previously said is the biggest challenge in combating traffickers: the ability of organised criminals to corrupt port staff through money and intimidation. He noted that port authorities were experimenting with staff training and access limitations.
Key defender takeaways:
-
Make sure your Security Operations Centre (SOC) monitors critical data and/or processes.
-
Enforce strict access controls, based on the principles of need-to-know and least privilege, to limit access to sensitive information
-
For high-risk roles, implement enhanced vetting and more frequent validation of access controls, as required by CER.
-
Train employees on how to recognise and resist corruption. Ensure a safe reporting culture, including a whistleblowing programme.
The time of blind trust in suppliers is behind us. Supply chain security starts with your own organisation.”
4. Supply chains amplify insider risk
Insider risk spans the entire supply chain and any cyber incident can quickly ripple across interconnected operations.
Authorities say the hacker compromised IT systems and container logistics at three ports: Antwerp, Rotterdam, and Barendrecht. While it’s not exactly clear how he gained access at Rotterdam, and Barendrecht, it’s believed he used a similar strategy to the attack in Antwerp. By exploiting vulnerabilities in digital and physical security at the ports, he breached linked systems that controlled customs inspections, container planning, and trucking operations.
The weaknesses that made this supply‑chain attack so easy to pull off aren’t unusual. Ports, logistics hubs, and industrial environments depend on tightly connected systems, which increases their exposure. We see too often that an organisation’s external partners and contractors don’t face the same security checks, monitoring, or access controls as internal staff. In today’s interconnected operations, insider risk must be treated as a shared responsibility across the entire supply chain.
Key defender takeaways:
-
Maintain clear visibility into which vendors and software (including open-source components) are in use, how they connect, and what access they have.
-
Enforce strict need-to-know policies that allow vendors to only access what’s necessary for their tasks for a limited period.
-
Ensure your Security Operations Centre (SOC) can isolate threats by disabling accounts and isolating endpoints.
-
Include critical suppliers in cyber resilience planning and training exercises.
- Clearly categorise your organisation’s supply chain risks and apply appropriate internal measures to the right type of threat.

Why Hybrid Threats Demand Holistic Defence
The cyberattack at the Port of Antwerp revealed how even a low-skilled threat actor can wreak havoc on critical systems and operational processes. The success of this attack hinged on insider access that could be manipulated across cyber, physical, and operational domains.
As such, the most important lesson for defenders is clear: effective security requires a holistic approach that connects prevention, detection, and response across IT, OT, physical operations, and supply chains. And, it must be grounded in a deep understanding of how your adversaries actually operate.
This is where Northwave brings unique value. We have 20 years of experience delivering preventative security, cyber threat intelligence, and hands-on incident response across Europe. Get in touch with us today to talk to our experts about how our holistic approach can safeguard your organisation from your current and future threats.
We are here for you
Need help with your cyber security or wondering how secure your business really is?
Get in touch and we will help you find the best solution.
