Arbitrary Free in Ivanti Secure Access Client Driver
Date: 10-11-2023
CVE NUMBER
CVE-2023-35080
CVSS SCORE
8.2 - CVSS:4.0/AV:L/AC:L/AT:N/PR:L/UI:N/VC:N/VI:L/VA:H/SC:N/SI:L/SA:H
SUMMARY
Ivanti's Secure Access Client (formerly Pulse Secure Access Client), an enterprise VPN client, is vulnerable to an arbitrary free vulnerability. The vulnerability exists inside one of the kernel drivers included in the software package named `jnprva.sys`. Exploiting this vulnerability could lead to a denial of service of the local system or corruption of kernel memory.
Impacted Versions
The bug has been present since at least 2018. At least the following versions are affected.
- Pulse Secure VPN version 9.1R18 and lower.
- Ivanti Secure Access version 22.6R1 and lower.
DETAILS
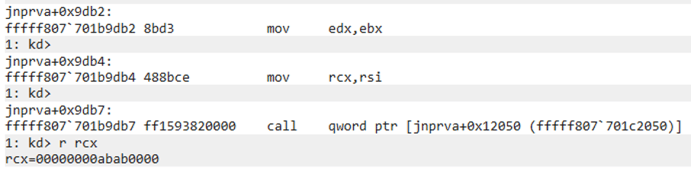
Several IOCTL handlers (for example `0x8000204C`) of the `jnprva.sys` driver call the `ExFreePoolWithTag` API on a user supplied address. If we pass, for example, the value `0xabab0000` inside of the correct field of the user-input, it is possible to reach the `ExFreePoolWithTag` with the user-supplied value:
The result of this could be blue screens or corruption of other kernel components.
TIMELINE
- 16-03-2023 – Initial notice to DIVD
- 20-03-2023 – First reply from Ivanti regarding their responsible disclosure policy
- 13-06-2023 – Northwave shares vulnerability details and PoC with Ivanti
- 09-09-2023 – Ivanti notifies Northwave of planned patch release date
- 17-10-2023 – Planned Vendor Patch Release (not achieved)
- 09-11-2023 – Vendor Patch Release
- 09-11-2023 – Public Release
REFERENCE
Ivanti Security Advisory: https://forums.ivanti.com/s/article/Security-fixes-included-in-the-latest-Ivanti-Secure-Access-Client-Release
CREDIT
Discovered by Tijme Gommers & Alex Oudenaarden of Northwave Cybersecurity.
Disclaimer
Northwave has made every effort to make this information accurate and reliable. However, the information provided is without warranty of any kind and its use is at the sole risk of the user. Northwave does not accept any responsibility or liability for the accuracy, content, completeness, legality or reliability of the information provided. We shall not be liable for any loss or damage of whatever nature, direct or indirect, consequential or other, whether arising in contract, tort or otherwise, which may arise as a result of your use of, or inability to use, this information or any additional information provided by us in direct or indirect relation to the information provided here.
